Checkpoint Smart Event Software Blade
From millions of real job salary data. 0 salary data. Average salary is Detailed starting salary, median salary, pay scale, bonus data report. CRN is the top news source for solution providers and the IT channel, providing up-to-date technology news, IT vendor and product reviews, channel partner resources. Find Semiconductor market research reports and Semiconductor industry analysis including industry overviews, market segmentation data, market share and growth.
Data Loss Prevention Software Blade. Check Point User. Check. Check Point User. Check empowers users to remediate incidents in real time. This innovative technology alerts users of suspected breaches for instant remediation and allows quick authorization of legitimate communications. User. Check improves security and raises awareness of data use policies by empowering users to self- administer incident handling- with options to send, discard or review the issue. Notifications occur in real- time via a pop- up from a thin agent or via a dedicated email sent to the end- user (no need to install agent).
Organizations benefit in several ways: Full prevention – enables a practical move from detection to data loss prevention. Self- educating system – educates and alerts users without involving IT/security personnel. Inspect SSL Encrypted Traffic. Scan and secure SSL encrypted traffic passing through the gateway.
- Our full product line frontplate visio stencils can help you with your network documentation or internal projects.
- Check Point Smart-1 appliances consolidate security management for superior threat visibility and control across Networks, Cloud and Mobile. Check Point Smart-1 smart.
- TheINQUIRER publishes daily news, reviews on the latest gadgets and devices, and INQdepth articles for tech buffs and hobbyists.
- You may have read recently how TSA and DHS have been making an aggressive effort to raise the bar on aviation security worldwide. Have you ever wondered what’s.
Home > Products > Manufacturers > CISCO. For complete on-line shopping and ordering or for current price and availability, please visit our eStore. Home > Products > Manufacturers > CHECK POINT. For complete on-line shopping and ordering or for current price and availability, please visit our eStore.
When traffic is passed through, the gateway decrypts the traffic with the sender’s public key, inspects and protects, then re- encrypts, sending the newly encrypted content to the receiver. For example, Gmail traffic is encrypted over HTTPS. It offers wide coverage of traffic transport types, including deep application awareness that protects data in motion, such as SMTP, HTTP and FTP data. DLP policies are created to define what to prevent and how to prevent it, by policy, by network segment, by gateway and by user- group.
Fingerprint Sensitive Files. DLP scans file repositories of sensitive files and match when a file from this repository (or part of it) leaves the organization. Simpsons Hit And Run Cheats.
With files matching, sensitive files are prevented from leaving the organization. Central Policy Management. DLP Software Blades are centrally managed with Check Point security management via a user- friendly interface. Centralized management offers unmatched leverage and control of security policies and enables organizations to use a single repository for user and group definitions, network objects, access rights and security policies across their entire security infrastructure. Unified access policies are enforced automatically throughout the distributed environment, empowering them to securely provision access from anywhere. Unified policy deployment across multiple gateways controls enforcement actions per policy; i. Policy management includes the following features and options: Selection of data type(s) and user group(s) – also using Active Directory.
Enable exceptions – allowed users. Traffic direction – enforce on outbound or inter- departmental traffic. Pre- defined policies and content data types. Incremental exposure of specific policies per different user groups. Integrated logging and event correlation.
Customization of internal quarantine. Granular protection control – easy- to- use protection profiles allow administrators to define signature and protection activation rules that match the security needs of their network assets. Predefined default and recommended profiles – provides immediate and easy out- of- the- box use with profiles tuned to optimize security or performance. Rapid and Flexible Deployment.
Organizations of any size can be protected from the start with pre- configured templates for immediate data loss prevention. A wide range of built- in policies and rules are included for common requirements, including regulatory compliance, intellectual property and acceptable use. The Check Point DLP Software Blade can be installed on any Check Point security gateway (based on Check Point appliances or open server platforms).
Deploy easily and rapidly on existing Check Point security gateways, saving time and reducing costs by leveraging existing security infrastructure. In addition, a full range of powerful and highly scalable DLP- 1 Appliances are available to align with any network security requirements. Crack Para Activar Windows Vista Business. Protect Against Data Breaches Both Externally and Internally. Check Point DLP controls sensitive information from leaving the company. Check Point DLP delivers exceptionally high accuracy in identifying sensitive data including Personally Identifiable Information (PII), compliance- related data (HIPAA, SOX, PCI, etc.) and confidential business data. This is achieved through the Multi. Spect technology, a strong 3- tier inspection engine that: Offers multi- parameter data classification and correlation – Multi- protocol inspection and enforcement inspects content flows and enforces policies in the most widely used TCP protocols including: SMTP, FTP, HTTP and webmail.
Pattern matching and file classification allows for the identification of content types regardless of the extension applied to the file or compression. Recognizes and protects sensitive forms – Includes file/ form matching (based on predefined templates)Identifies unconventional business communication behavior. Leverages out- of- the- box best practice policies. In addition, an open scripting language is available for creating custom data types.
This unique flexibility provides virtually unlimited support for protecting sensitive data. Watermarking. The DLP Software Blade has a new document watermark feature in R7. Flexible choice of visible watermarks to Microsoft Office documents: Page placement. Text formatting options such as semitransparent, diagonal, size, font, color, text direction. Customize watermark with fields such as sender, recipient, name of document and/or date sent. Add encrypted hidden watermarks: No change in visible document layout. Can be identified in DLP scans.
Used for forensics analysis to track leaked documents. Whitelist Files and Repositories. Define a list of files and repositories so users do not have to remediate files that are safe for distribution.
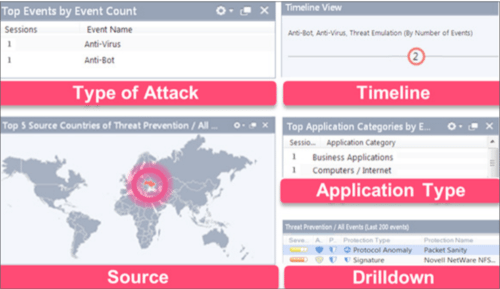
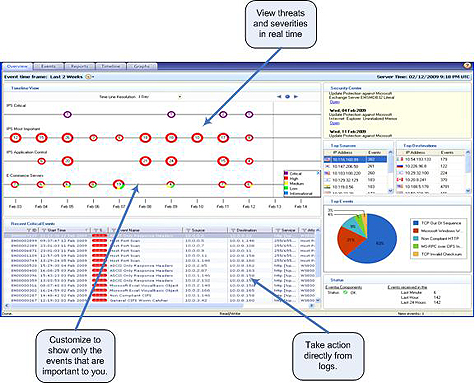
Event Management. Separating the needle from the haystack, Smart. Event for DLP monitors and reports only what is important.
Event management includes the following features and options: Real- time and history graphing and reporting of DLP events. Easy incident correlation. Graphical incident timelines. Easily configured custom views. Event/incident management workflow. For more details, see Check Point Smart.
Event Software Blade. Integrated into Check Point Software Blade Architecture.
The DLP Software Blade is integrated into the Software Blade Architecture. It can be easily and rapidly activated on existing Check Point Security Gateways saving time and reducing costs by leveraging existing security infrastructure.